Over the years software as a service (SaaS), platform as a service (PaaS) and infrastructure as a service (IaaS) have really taken off with many organisations utilising one or all of these deployment models. Naturally, these deployment models come with their own security threats to consider.
Cloud computing is the on-demand delivery of shared IT resources over the Internet such as computing power, storage, and databases, on an as-needed basis. The fact that cloud systems are exposed to the internet makes them low-hanging fruit for cyber-attackers. Cloud security threats can take on many forms, however, Cloud Misconfiguration is the leading cause of data breaches on the cloud.
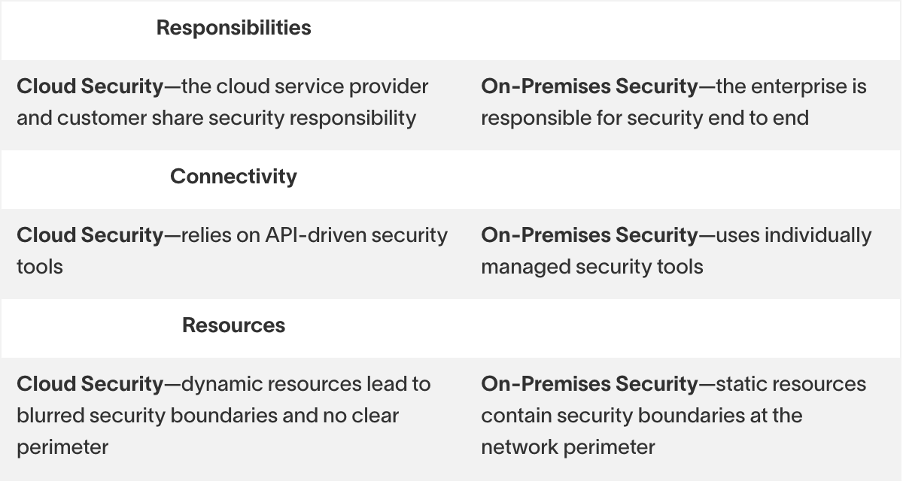
The first step in tackling cloud security is in understanding that it is different from on-premise security. Exabeam clarifies these differences by illustrating how responsibility is divided between the cloud users and cloud providers across different cloud models.
Exabeam: Cloud Security: Principles, Solutions, and Architectures
From the above, it is clear that as much as cloud systems have their advantages, they come at a cost beyond what you are paying for them. For instance, it’s of great advantage that you have access to dynamic resources on-demand, but if what you’re meant to be securing is constantly changing in accordance to your demand, securing it requires more effort. It is important to have a clear understanding of what your organisation’s responsibilities. Unfortunately, some of these may not be so obvious.
Given that cloud services are offered by service providers that handle the hardware and back-end portions of the cloud, it’s easy to assume that they are also responsible for every aspect of security. In reality, that kind of assumption is what has led many organisations into the pitfall of cloud misconfiguration. You can never be too secure, so no matter what kind of setup you employ, you need to adhere to a very important principle of cloud security: shared responsibility.
While the service provider offers security for the underlying infrastructure, the organisation is responsible for securing the data itself. It is key to take all of this into consideration when selecting your cloud service provider, and more importantly, the cybersecurity partner that will help you secure your data.
The Exabeam Security Management Platform (SMP) offers a comprehensive solution for protecting your digital resources in the cloud and on-premises. Exabeam provides the connectivity necessary to monitor all your cloud services, including: Cloud services—such as Salesforce, Office 365, and Box.
Exabeam also monitors your cloud services at scale, providing unlimited logging for the ingestion and modelling cloud data. Plus it scans for anomalous activity throughout your cloud infrastructure through intelligent and automated detection.
Contact DataGroupIT to find out more about how Exabeam can be utilised in your organisation to protect what matters the most to you, your data.
About DataGroutIT
DataGroupIT is Africa’s leading Value-Added Distributor (VAD). By partnering with the best selection of established and emerging technology vendors across the globe, we, provide complex solutions for any size business, including Enterprise and SME markets across the African continent.
Our product portfolio offers comprehensive solutions for IT Security, Infrastructure and Enterprise Software.
We are fully committed to our business partners. Channels & vendors success is our #1 mission. Our professional teams across Africa deliver exceptional sales, presale, logistic, marketing and financial support that create the ultimate platform to accelerate our business partners’ success.




